UFW (Uncomplicated Firewall) is a simple-to-use firewall utility with plenty of options for all kinds of users. It is actually an interface for iptables, which is the classic low-level tool (and harder to get comfortable with) to set up rules for your network. Why should you …
In this post, we’re going to talk about this error which you may see while trying to play Spotify music on your Windows 11/10 PC – A firewall may be blocking Spotify, Error code 30. Spotify is among the best platform to stream music online. It …
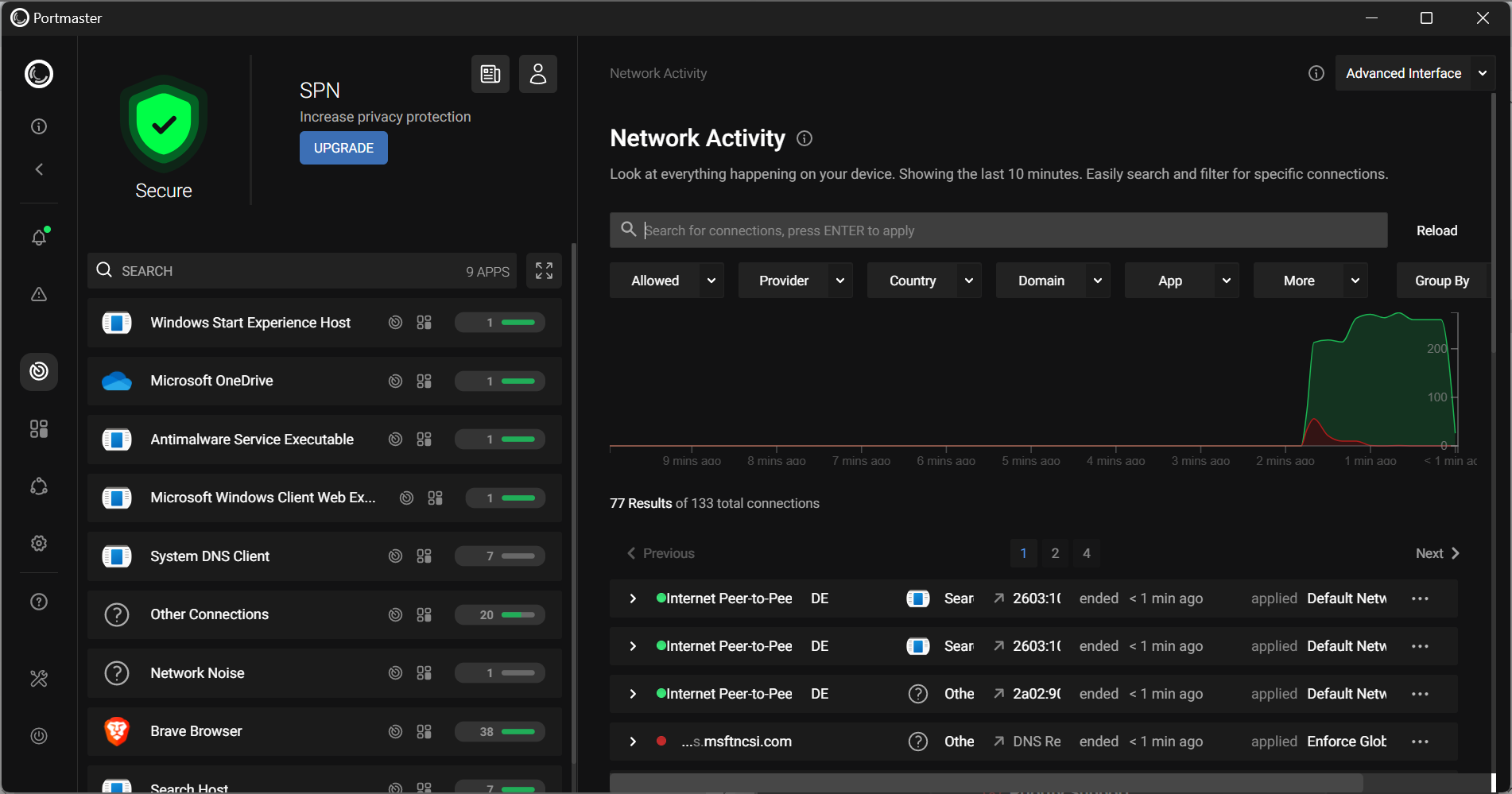
Most people view the internet as a powerful tool for accessing information in an instant, but advertising companies see it in just the same way — often utilizing the very internet connection you depend on for said information to track your every move and report back …
As you make the move from Microsoft on-premises infrastructure to the cloud, you’ll move from Group Policy management of your endpoints to MDM management. This move isn’t always a “lift and shift” process because there isn’t always a 1-to-1 relationship between the settings available in …
Windows Firewall Control 5 is the latest version of the popular Windows program that gives you better firewall management options and control. The program is available as a free, somewhat limited, version, and a version that is unlocked when you make a donation. Windows Firewall Control …
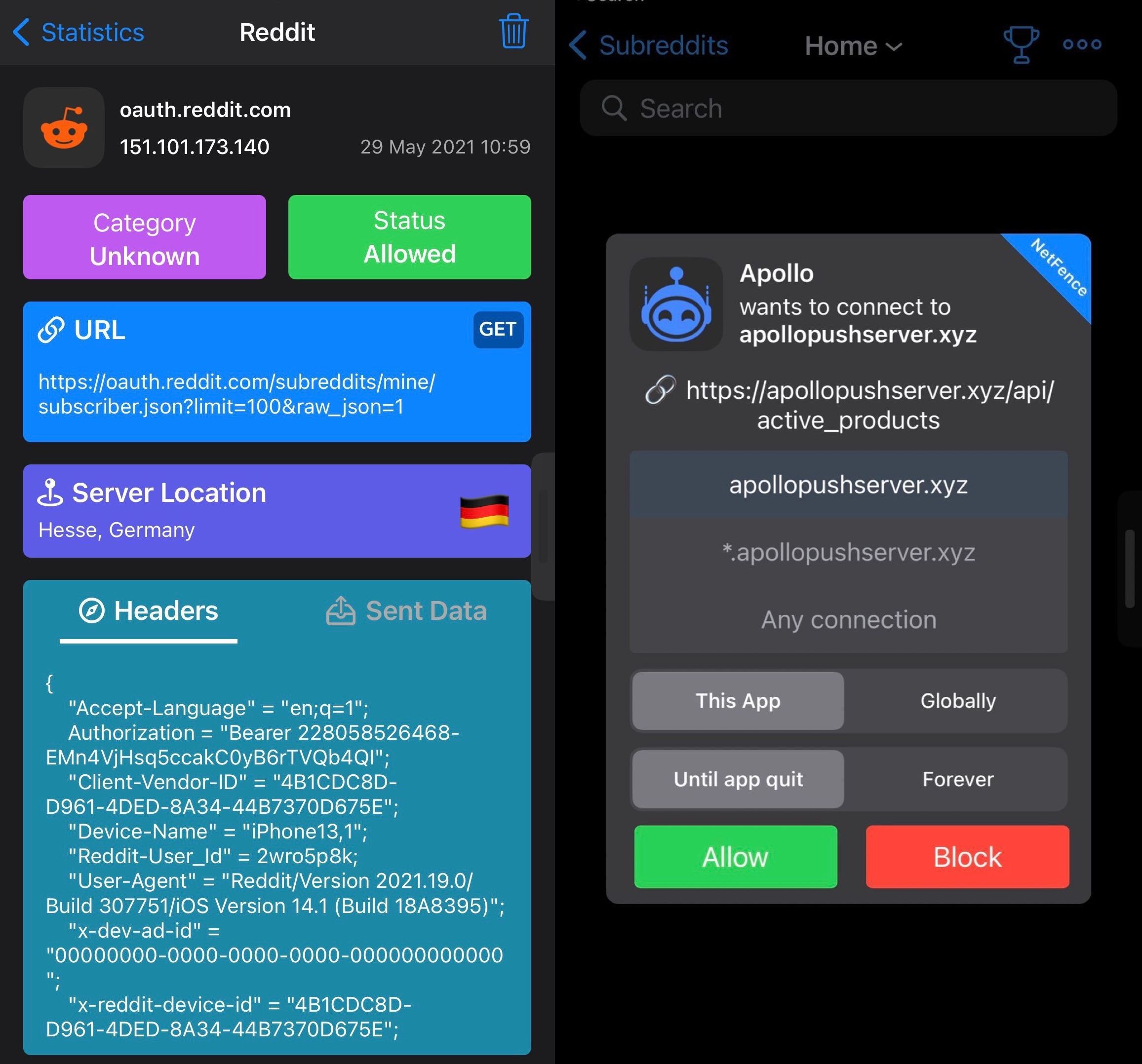
Little Snitch is a traditional software firewall for macOS. You can use it to monitor applications, preventing or permitting them to connect to attached networks through advanced rules. OpenSnitch is a GNU/Linux port of the Little Snitch application firewall written in Python. The software is still …
In this tutorial, we are going to show you how to set up a firewall with iptables on a Linux VPS running Ubuntu or CentOS as an operating system. Iptables is an administration tool for IPv4 packet filtering and NAT and it is used to …
Windows Firewall is one of the most important aspects of every Windows operating system. The firewall is there to aid in blocking attackers from gaining access to sections of the operating system that could prove dangerous. Now, from what we have come to learn of …

![Using Firewall With UFW in Ubuntu Linux [Beginner’s Guide] Using Firewall With UFW in Ubuntu Linux [Beginner’s Guide]](https://techgit.net/wp-content/uploads/2022/11/check-ufw-status-1.png)