This week OpenSSL has released fixes for a high severity Denial of Service (DoS) vulnerability impacting the open source project.
U.S. DHS Cybersecurity and Infrastructure Security Agency (CISA) has warned admins to upgrade their vulnerable OpenSSL instances immediately.
Caused by null pointers in SSL certificate name validation
The high severity vulnerability tracked as CVE-2020-1971, stems from a NULL pointer dereferencing issue.
As specified by the X.509 standard, SSL certificates use the GeneralName type in various places to represent different types of names.
A GeneralName object can be an IP address, a DNS name, a URL identifier, or even something called an “EDIPartyName.”
When validating X.509 SSL certificates, OpenSSL uses the GENERAL_NAME_cmp function to compare two GeneralName fields.
If both fields being compared contain an EDIPartyName, however, OpenSSL can crash due to a NULL pointer dereferencing bug.
For example, OpenSSL advisory states, one place where the GENERAL_NAME_cmp function is used is when OpenSSL validates a certificate’s CRL (Certificate Revocation List) distribution point field.
Most SSL certificates contain within themselves what’s called a CRL Distribution Point field.
This field specifies the location where the certificate’s issuer publishes a list of revoked certificates that can be checked by the client, such as a web browser.
As shown below, BleepingComputer’s SSL certificate issuing authority Sectigo has specified its CRL Distribution Pointas a URL.
This means, when you visit https://bleepingcomputer.com, your web browser receiving our certificate should ideally be validating it against the CRL provided at this URL embedded within the certificate.
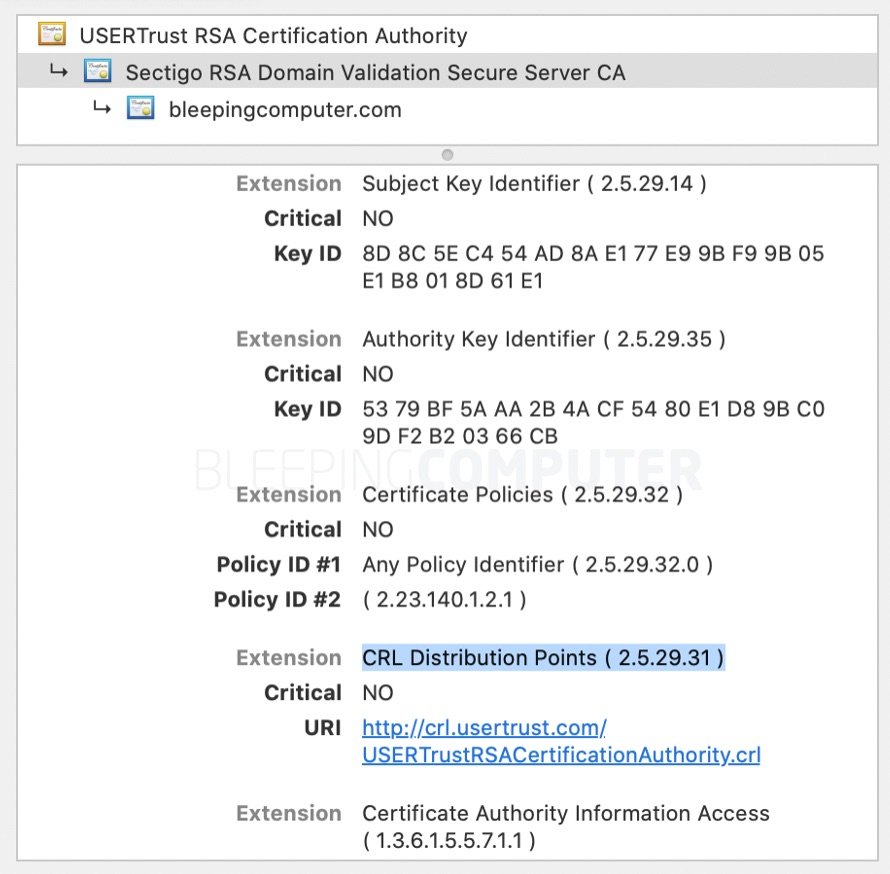
However, the distribution point comprises a CRL location which is of the GenericName type (pages 46-48 of RFC 5280).
Recall, GenericName need not be a URL and can also be specified as an IP address, or an EDIPartyName.
If an attacker is able to craft an SSL certificate containing an EDIPartyName field to specify the CRL details, and a malicious CRL itself, the GENERAL_NAME_cmp function when comparing the two fields may trigger an application crash and cause a Denial of Service (DoS) condition.
But, this is just one of the ways this vulnerability can be exploited.
Another place where GENERAL_NAME_cmp function is being used in OpenSSL is when comparing the timestamp response token signer to the timestamp authority name.
CISA urging admins to upgrade
Reported on November 9th, 2020, by David Benjamin of Google, this vulnerability impacts all versions of OpenSSL 1.0.2 and 1.1.1 (before 1.1.1i).
Following an analysis of the bug, a fix was deployed by Matt Caswell of OpenSSL in version 1.1.1i.
In 2014, critical heartbleed vulnerability in OpenSSL had made headlines following rampant exploits in the wild.
This is perhaps why CISA has issued a security advisory for CVE-2020-1971 prompting server admins to immediately upgrade their OpenSSL instances.
Users of OpenSSL 1.1.1 can upgrade to the 1.1.1i version. Product support for OpenSSL 1.0.2 and earlier versions has reached end-of-life and as such only premium users are being provided with the patched 1.0.2x version. General users should upgrade to the 1.1.1i version.
