
To find the process ID of a Linux process, use the pidof command, like this: “pidof examplename”. If you only know part of the PID name, you can use “pgrep examplenamefragment” instead. Replace “examplename” and “examplenamefragment” with the terms you want to search for.
Working with a Linux process often means knowing its process ID, or PID. It’s a unique number given to each piece of running software. Here are two ways to find out what it is.
What Is a Linux Process ID?
Internally, Linux keeps track of its running process by allocating them a unique ID number, called the process ID, or PID. Every running application, utility, and daemon has a PID.
PIDs are simple integer values. A newly-started process will receive a PID one higher than the last PID that was issued. So the process with the highest PID is the newest—that is, most recently—launched process. That carries on until the system hits the maximum value for a PID.
The upper limit for a PID is 32768. Once that figure is reached, Linux goes back to the start and looks for a PID that has become free because the process that previously owned it has terminated.
The process with a PID of 1 is the first process that is launched when Linux is launched by the boot-up processes. On systemd-based systems that’ll be systemd . On other systems it is likely to be init, although some Linux distributions use alternatives such as OpenRc or s6.
Sometimes it’s useful to discover the PID of a process, usually because you want to perform some action on that process. Here are two different methods of finding the PID of a process when you know the name of the process.
How to Get a Linux PID With the pidof Command
The pidof command can be thought of as the combination of “PID” and “of.” It’s like asking what’s the PID of this process? If we use the command with no parameters it doesn’t do anything. It silently returns you to the command prompt. We need to specify a process name.
pidof bash

pidof tells us the PID of the Bash shell is 8304. We can verify that with the ps command. All we need to do is call ps with no parameters. It’ll report on the processes that are running in the current session.
ps

Because ps reports on all the processes it can find, which will include itself, it tells us there’s a bash process and a ps process running. As we’d expect, the bash process has the same PID that pidof reported on.
If you have more than one terminal window open, pidof will report on them all.
pidof bash

Note that the PIDs are listed from highest to lowest or, in other words, from most recent to the oldest.
What this doesn’t show is that you might not be the owner of all of those processes. pidof finds all processes with matching names, regardless of who owns them. Let’s look deeper by piping the output into grep. We’re using the -e (select all processes) and the -f (full listing) options with ps .
ps -ef | grep bash

Two of the bash processes belong to user dave, the third belongs to user mary.
Sometimes one application will generate a lot of processes, each of which receives its own PID. This is what we get with Google Chrome.
pidof chrome

By default, pidof reports on all processes. If we want, we can ask for just the most recent of those processes. The -s (single shot) option does just that.
pidof -s chrome

To use the kill command to manually kill all of the chrome processes would be tedious. If we capture the list of processes into a variable, we can pass that variable to the kill command. The kill command can accept multiple PIDs on its command, so it happily accepts our input and kills all of the processes for us.
pid=$(pidof chrome)
echo $pid
kill $pid
pidof chrome
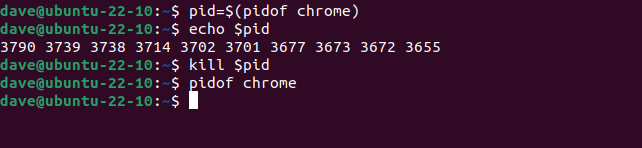
The first command collects the output from pidof and assigns it to our variable, which we’re naming pid. We don’t need to echo it to the screen, we’re just doing that to show what our variable holds.
We pass the variable to the kill command, then use pidof once more to check whether any Chrome processes remain. They have all been killed.
One quirk of pidof is that it won’t return the PID of a shell script. It returns the PID of the bash shell that is running the script. To see the shell that is running a script, we need to use the -x (scripts) option.
pidof -x sleep-loop.sh
ps -e | grep bash

pidof returns the PID of a bash shell, and ps shows us there are two shells running. One is the shell running the pidof command, and the other is the shell running the script.
How to Find PIDs With the pgrep Command in Linux
The pgrep command works a little like pidof in getting process IDs in Linux. However, it doesn’t just find processes that exactly match the search clue, it also returns the PIDs of any processes whose name contains the search text.
Here’s an example on a computer that has Firefox running on it.
pgrep firefox
pgrep fire
pgrep fox
pgrep refo

All of these commands find the Firefox process and return the PID. But if you’d entered the command:
pgrep refo
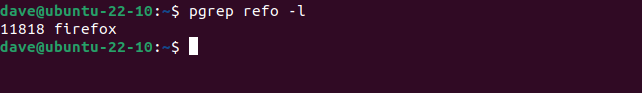
On its own, how would you know if pgrep had found Firefox and not, say, a dameon called preformd?
If you add the -l (list name) option, pgrep will list the process name alongside the PID.
pgrep refo -l
If there are multiple instances of a matching process, they are all listed.
pgrep bash

Note that they are listed in ascending order, which is the opposite order to the output from pidof. They are listed from the oldest process to newest process. As we saw with pidof, not all of the listed processes necessarily belong to you.
The -u (user id) option lets you search for processes that match the search text, and are owned by the named user.
pgrep bash -u dave

This time we see three bash processes in the results. The other is being used by mary.
pgrep bash -u mary

We can string usernames together as a comma-separated list.
pgrep bash -u dave,mary -l

And we can ask to see all processes for a specific user.
pgrep -u dave -l

To see the full command line, use the -a (full list) option.
pgrep -u dave -a

A Word About PID Ownership
Not all system processes are owned by the root user. Many are, of course, but not all of them. For example, this command works:
pgrep avahi-daemon
But this command fails.
pgrep -u root avahi-daemon
It fails because root does not own that process. The actual owner is a system user called “avahi.” Using the correct user name, the command works.
pgrep -u avahi avahi-daemon
It’s a little gotcha to watch out for.
| Linux Commands | |
| Files | tar · pv · cat · tac · chmod · grep · diff · sed · ar · man · pushd · popd · fsck · testdisk · seq · fd · pandoc · cd · $PATH · awk · join · jq · fold · uniq · journalctl · tail · stat · ls · fstab · echo · less · chgrp · chown · rev · look · strings · type · rename · zip · unzip · mount · umount · install · fdisk · mkfs · rm · rmdir · rsync · df · gpg · vi · nano · mkdir · du · ln · patch · convert · rclone · shred · srm |
| Processes | alias · screen · top · nice · renice · progress · strace · systemd · tmux · chsh · history · at · batch · free · which · dmesg · chfn · usermod · ps · chroot · xargs · tty · pinky · lsof · vmstat · timeout · wall · yes · kill · sleep · sudo · su · time · groupadd · usermod · groups · lshw · shutdown · reboot · halt · poweroff · passwd · lscpu · crontab · date · bg · fg |
| Networking | netstat · ping · traceroute · ip · ss · whois · fail2ban · bmon · dig · finger · nmap · ftp · curl · wget · who · whoami · w · iptables · ssh-keygen · ufw |
