A group of hackers was able to infect iOS, Android, and Windows by exploiting close to 11 zero-day vulnerabilities in a span of nine months. This has been discovered by Google’s Project Zero team, which takes care of security issues on various platforms.
It is suggested that all this was done by using compromised websites to get access to the operating systems. Read on to know more about it.
iOS, Android, Windows exploited
It is revealed (via ArsTechnica) that the hackers used a mixture of exploitation techniques and vulnerability types to perform zero-day vulnerabilities and become, what Google researchers call ‘highly sophisticated.’
The whole security breach started in February 2020 and went on until October 20, totalling up to 11 zero-day attacks.
For those who don’t know, a zero-day vulnerability is the one that remains unknown to the people who are interested in fixing it. Until a fix is out, hackers can easily exploit to infect the devices, OS, software in question.
What happened?
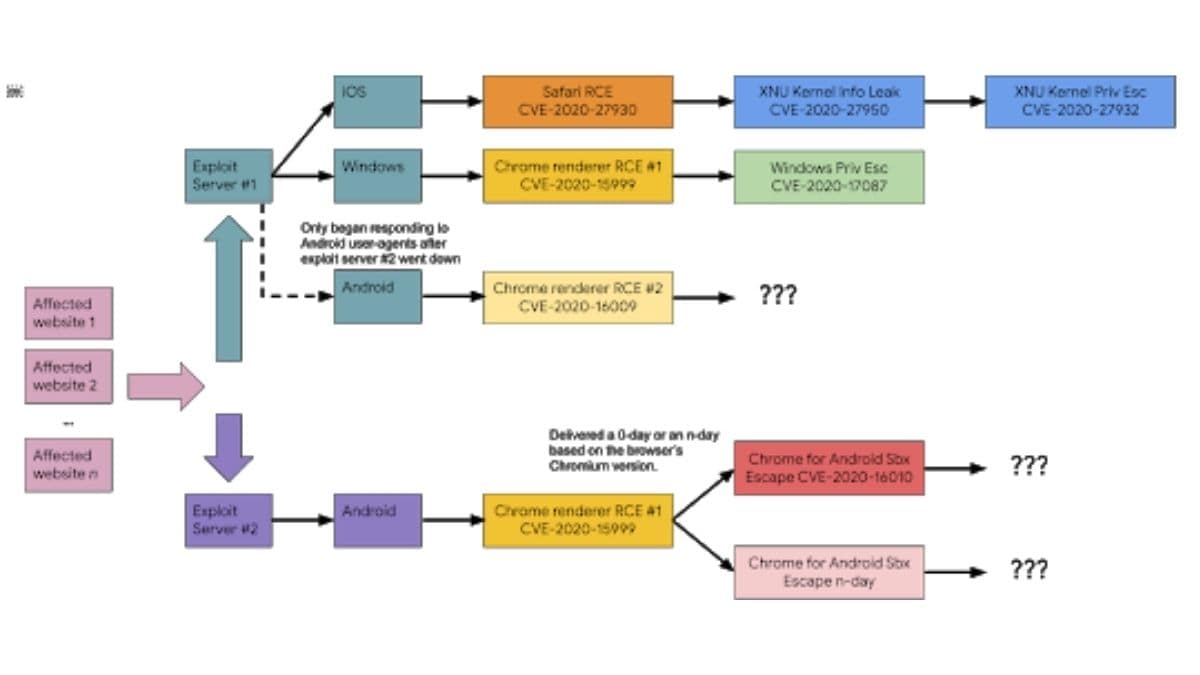
Hackers used malicious websites (by inflicting watering-hole attacks on them) to inject the iOS, Android, and Windows devices with malicious codes via an iFrame, which was different for different devices. While one server focused on Windows and Android devices, the other one exploited the iOS devices.
Image: Google Project Zero
Google researchers, via the blog post, said, “In October 2020, we discovered that the actor from the February 2020 campaign came back with the next iteration of their campaign: a couple of dozen websites redirecting to an exploit server. Once our analysis began, we discovered links to a second exploit server on the same website. After initial fingerprinting (appearing to be based on the origin of the IP address and the user-agent), an iframe was injected into the website pointing to one of the two exploit servers. ”
It is said that the hackers’ ability to bypass the security layers of these ‘well-fortified OSs is quite a skill. This is further proven after the hackers were able to infect Google Chrome despite Google patching the exploit in February.
This means that even though your device is up-to-date, there are chances of it getting prone to a security breach. Hence, it’s best advised to avoid using websites or apps that prove suspicious.