In February Microsoft disabled DNS-over-HTTPS (DoH) in all Edge channels due to performance issues.
With regular DNS, if you are visiting a site using HTTPS, your DNS query is sent over an unencrypted connection. That means that even if you are browsing a secure site, anyone listening to packets on the network knows you are attempting to visit that site.
The second problem with unencrypted DNS is that it is easy for a Man-In-The-Middle to change DNS answers to route unsuspecting visitors to their phishing, malware or surveillance site. DoH offers DNS resolution over an HTTPS endpoint. When users can choose DNS over HTTPS endpoint instead of sending DNS queries over plaintext it increased security and privacy.
The good news is that Microsoft has restored DoH to all pre-stable channels (Canary, Dev, Beta) so users can once again select an alternate and secure DNS provider for their browser.
Microsoft rightly notes that this is not completely a decision without consequence, as it can cause issues when browsing some local or enterprise sites for example.
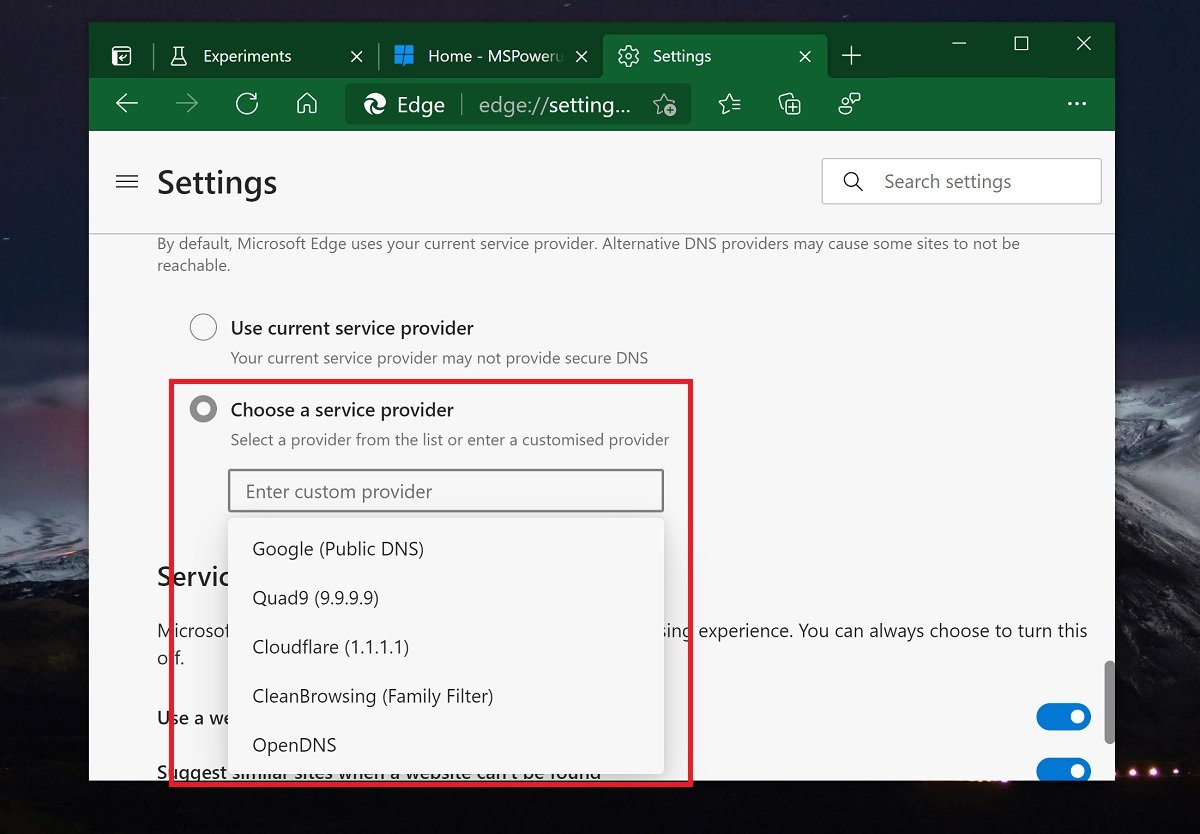
To experiment with this in Edge, try out a new DNS provider by going to Edge Settings> Privacy and scroll to Security > Use secure DNS to specify how to lookup the network address for websites.
via Techdows