Microsoft has had a troubled year dealing with Windows Updates causing printer issues. The latest problem that has affected printers is called PrintNightmare, which is a remote code execution vulnerability.
Martin wrote an article about this, where he explains a couple of workarounds to deal with the issue that exploits the Print Spooler service.
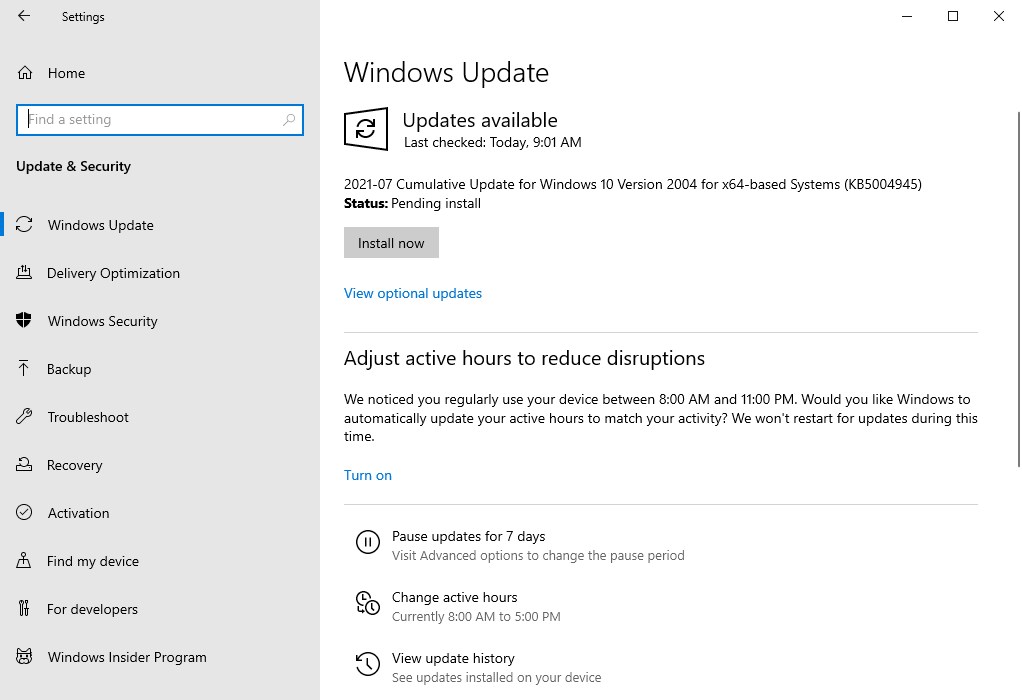
Microsoft is rolling out an emergency Windows Update called KB5004945 to address the PrintNightmare vulnerabilities. The CVE-2021-34527 security advisory, confirms that the issue affects all versions of Windows. The announcement page for the update recommends users to install the update as soon as possible.
The summary for the patch states that it fixes the remote code execution vulnerabilities.
KB5005010 Update
The release notes for a second patch, called KB5005010, tell us that the update will prevent non-administrator users from installing new printer drivers. The operating system will only allow signed printer drivers for delegates, while non-signed drivers will require admin privileges. The security fix changes the Point and Print policy’s registry value to 0, to prevent unauthorized elevation of privileges.
The July 2021 out-of-band update will appear as a cumulative update. It is also available from the Microsoft Windows Update Catalog. You will need to restart the computer to finish patching the computer. It bumped the version number from Windows 10 2004 Build 19041.1055 to Build 19041.1083. The update isn’t available for the Windows 11 Insider Preview build that was released a week ago, and rumors suggest that this could be one of the reasons by the Beta release that was scheduled to be released this week has been postponed.
KB5004945 is preventing Zebra printers from printing
Users at the Reddit’s sysadmin forums have reported that the KB5004945 update is preventing Zebra printers from printing documents, and that the company’s customer support has instructed users to roll back (aka uninstall) the update, to get the devices working.
Hackers say they have bypassed the patch
While it appears that the printing security woes have been resolved, security researchers say they have bypassed the security patches that were included in the KB5004945 emergency update. If the computer has already been configured to use the Point and Print policy, hackers can invoke the LPE (local privilege escalation) or RCE (Remote Code Execution) to gain access to the system. The company has told Bleeping Computer that it is investigating the bypasses.
The researchers term the update as unsatisfactory (or incomplete), as in it doesn’t protect the systems completely, and have advised users to keep the Print Spooler service disabled, until a proper fix is issued by Microsoft.
I’m no security expert, but from my understanding, the bypass only appears to be valid when the Point and Print policy has been enabled, and has been configured not to show the elevation prompt. However, Microsoft’s support page clearly indicates that the registry key for the policy does not exist, and that the elevation prompt is not hidden, which theoretically means that users should be safe if they have installed the patch.
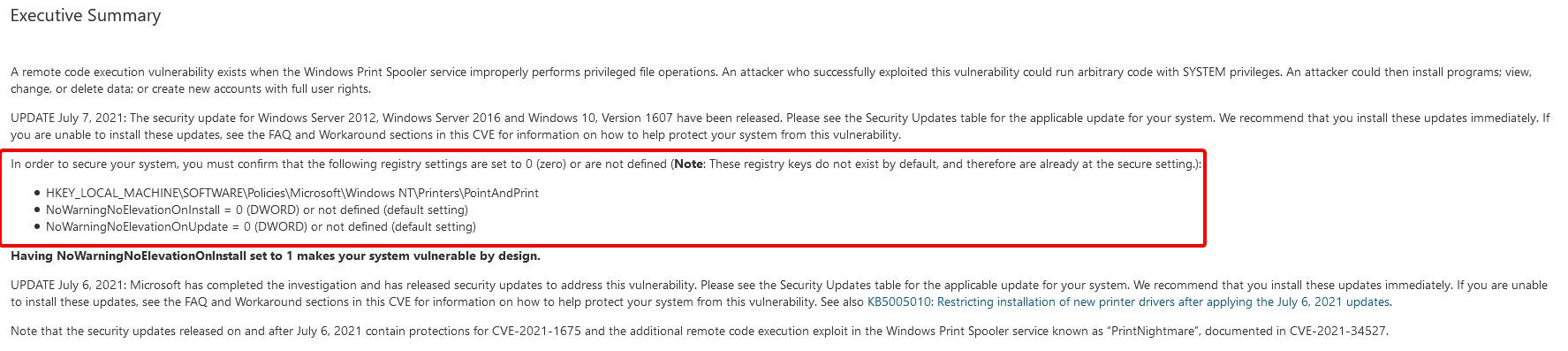
To make sure you aren’t affected, you can manually create the registry key as follows,
HKEY_LOCAL_MACHINESOFTWAREPoliciesMicrosoftWindows NTPrintersPointAndPrint
NoWarningNoElevationOnInstall = 0 (DWORD) or not defined (default setting)
NoWarningNoElevationOnUpdate = 0 (DWORD) or not defined (default setting)
Are you facing any printer issues since installing the KB5004945 update?
The post Microsoft rolls out KB5004945 emergency Windows Update to fix PrintNightmare vulnerabilities, but it seems to be affecting Zebra printers appeared first on gHacks Technology News.
