News about ChatGPT is everywhere, making it one of the biggest topics in the tech community these days and a well-known AI creation around the globe. With this, it is no surprise that threat actors would want to exploit this opportunity as a lure to target unknowing Windows to Android users.
A report by researchers at Cyble (via Bleeping Computer) shows different typosquatted domains posing as ChatGPT portals and websites. Apart from that, it said there are currently 50 fake and malicious applications that “belong to different malware families, such as potentially unwanted programs, adware, spyware, billing fraud, etc.” Apparently, these apps use the same logos from OpenAI and ChatGPT, giving them a better disguise to fool victims. In addition to this, Cyble said threat actors are also leveraging social media platforms to promote their phishing websites through a fake OpenAI social media page.
In the shared screenshot, the “Chat GPT AI” page has at least 3.5K followers and several posts. Cyble noted that the actors are trying to make the page look credible by posting various content. For instance, besides videos, the page features other creations from OpenAI, such as Jukebox. However, the ultimate goal of all these posts is to lead users to click links included in them, which will bring victims to different phishing pages and trick them into downloading malicious files into their devices.
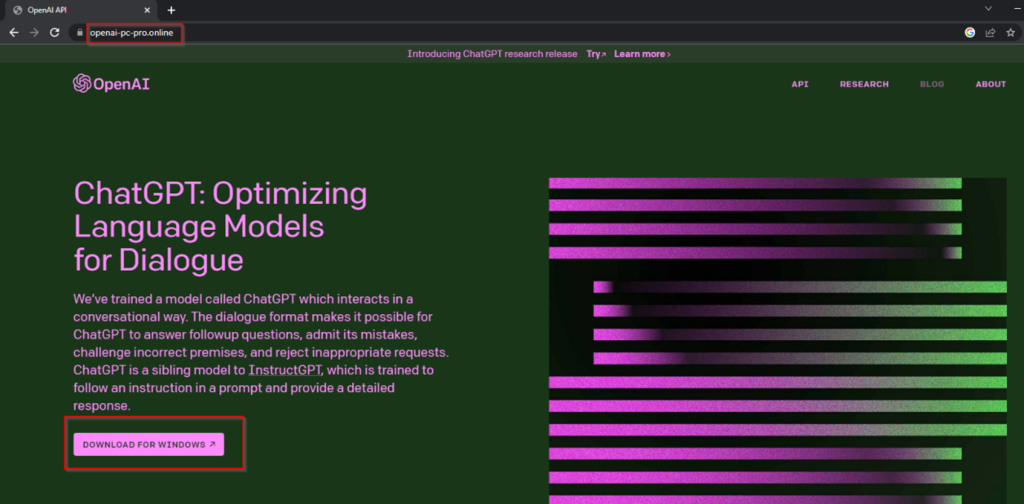
Unfortunately, many might fall victim to this campaign. Apart from using OpenAI and ChatGPT logos, many elements in the pages copy those in the legitimate OpenAI website, making the place a truly dangerous trap. For example, the domain “openai-pc-pro[.]online” is fashioned with OpenAI’s distinguishing green and purple designs. It offers a direct “DOWNLOAD FOR WINDOWS” button, complete with product descriptions. Clicking it, however, will download a compressed file containing an executable file.
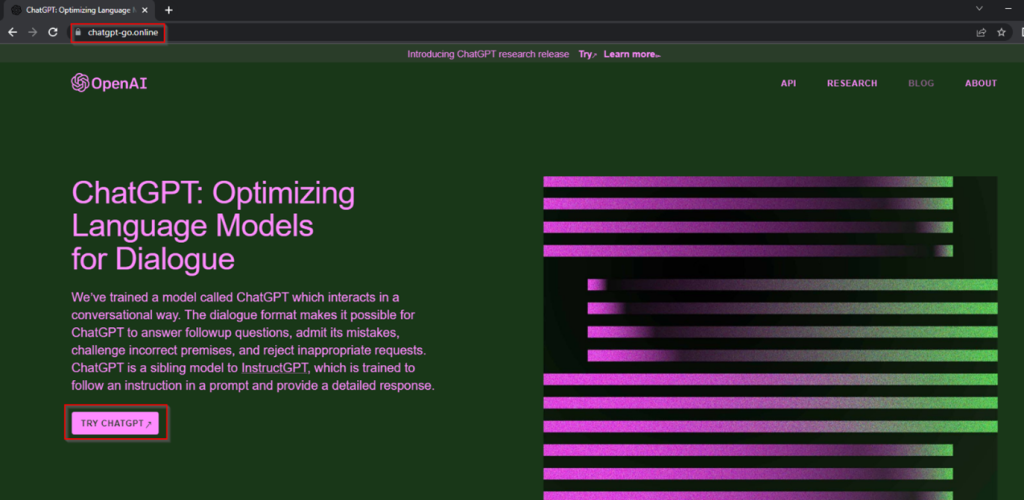
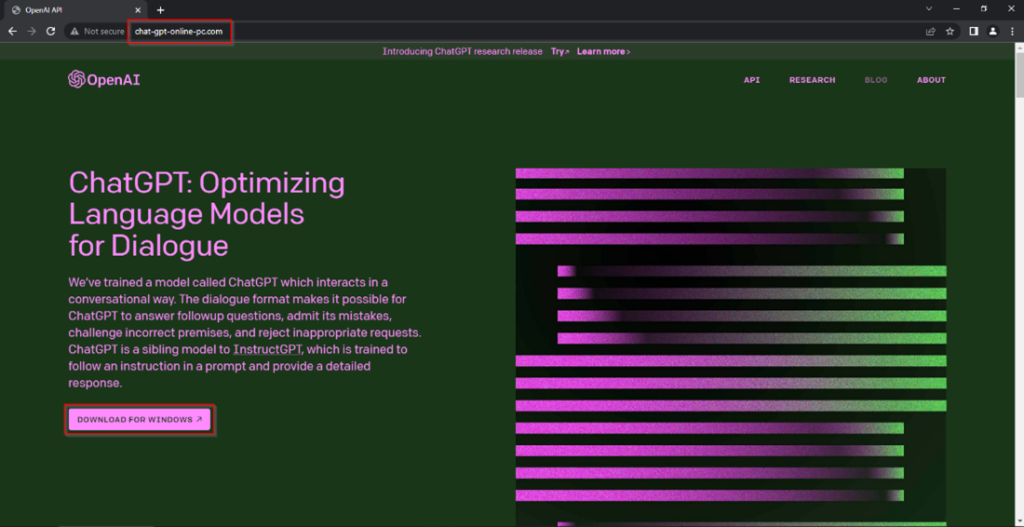
Apart from openai-pc-pro[.]online, other domains mentioned in the report include chatgpt-go[.]online and chat-gpt-online-pc[.]com. According to the report, the phishing sites are also distributing malware families, such as Lumma Stealer, Aurora Stealer, clipper malware, and more. Cyble also spotted a page named pay[.]chatgptftw[.]com designed to steal credit card information from victims. It also said that it identified several SMS fraud applications masquerading as ChatGPT, which is also designed for committing financial fraud.
In a more alarming situation, the fake ChatGPT apps were also spotted on Google Play and other third-party app stores, as shared by cybersecurity analyst and security researcher Dominic Alvieri. The analyst, however, said that the items are now removed from Google Play Store.
With ChatGPT’s growing fame, more and more malicious campaigns revolving around the tech might continue for years. While there is no all-in-one solution that will prevent anyone from experiencing them, cautious online actions should be effective enough to save you from falling into deep malware pits. And as suggested by Cyble and mentioned by other security experts before, being observant and only trusting legitimate websites are the first steps to do that.
