
For maximum security, you should use WPA2 (AES) if you have older devices on your network and WPA3 if you have a newer router and newer devices that support it.
Your Wi-Fi router offers encryption options like WPA2-PSK (TKIP), WPA2-PSK (AES), and WPA2-PSK (TKIP/AES) and even, if it’s modern enough, WPA3 (AES). It can be a bit confusing, and if you choose the wrong one, you’ll have a slower, less-secure network. Here’s what you need to know.
WPA2 vs. WEP, WPA, and WPA3
When you read about Wi-Fi security, the primary focus is usually on the type of encryption used to secure the wireless connection. That makes sense, after all, because, by the very nature of a Wi-Fi router, all communications between your client device (like your smartphone or laptop) and the router are flung through the open air. Anybody in range of your router can snoop on that communication or even gain access to your router if the wireless connection is insecure.
This wireless connection is secured using security algorithms specifically designed for Wi-Fi. These algorithms aren’t strictly just encryption (though that’s a crucial component) but include additional functions that govern how keys are exchanged and verified, and more.
Wired Equivalent Privacy (WEP), Wi-Fi Protected Access (WPA), and Wi-Fi Protected Access II (WPA2) are the primary security algorithms you’ll see when setting up a wireless network. If you have a newer router, you may also see Wi-Fi Protected Access III (WPA3), too.
WEP is the oldest and has proven to be vulnerable as more and more security flaws have been discovered. WPA improved security but is now also considered vulnerable to intrusion.
WPA2, while imperfect, is more secure than WEP or WPA and is one of the most widely used Wi-Fi security algorithms. WPA and WPA2 networks can use one of two encryption protocols, Temporal Key Integrity Protocol (TKIP) and Advanced Encryption Standard (AES). We’ll look at the difference between those two encryption protocols in a moment.
Finally, WPA3 networks only use the AES encryption protocol. Although introduced in 2018, WPA3 still doesn’t have widespread adoption.
AES vs. TKIP
TKIP and AES are two different types of encryption that can be used by a Wi-Fi network. TKIP is actually an older encryption protocol introduced with WPA to replace the very-insecure WEP encryption at the time. TKIP is actually quite similar to WEP encryption. TKIP is no longer considered secure and is now deprecated. In other words, you shouldn’t be using it.
AES is a more secure encryption protocol introduced with WPA2. AES isn’t some creaky standard developed specifically for Wi-Fi networks, either. It’s a serious worldwide encryption standard that’s even been adopted by the US government.
For example, when you encrypt a hard drive with TrueCrypt, it can use AES encryption for that. Window’s built-in encryption tool BitLocker also uses AES, as does macOS’s tool FileVault. AES is generally considered quite secure, and the main weaknesses would be brute-force attacks (prevented by using a strong passphrase) and security weaknesses in other aspects of WPA2.
The short version is that TKIP is an older encryption standard used by the WPA standard. AES is a newer Wi-Fi encryption solution used by the new-and-secure WPA2 standard. In theory, that’s the end of it. But, depending on your router, just choosing WPA2 may not be good enough.
While WPA2 is supposed to use AES for optimal security, it can also use TKIP, where backward compatibility with legacy devices is needed. In such a state, devices that support WPA2 will connect with WPA2, and devices that support WPA will connect with WPA. So “WPA2” doesn’t always mean WPA2-AES. However, on devices without a visible “TKIP” or “AES” option, WPA2 is generally synonymous with WPA2-AES.
Wi-Fi Security Modes Explained: Which Should You Use?
Confused yet? Don’t feel bad if you are. The world of Wi-Fi security is pretty arcane if you’re not a diehard network geek. Thankfully you don’t need to understand the intricacies of how security protocols and handshakes changed between all the generations of Wi-Fi.
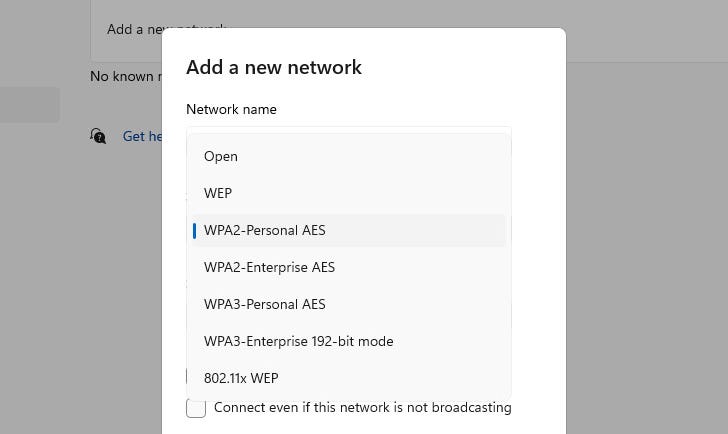
You just need to review our list below and select the most secure option that works with all of your hardware and devices. To help you avoid older and insecure options, we’ve flagged them with [Deprecated] after their name.
And, to be clear, we’re not arbitrarily gatekeeping these protocols and declaring them deprecated based on our opinions. Both Microsoft and Apple have designated them as such, too, which is why your Windows laptop warns you when a Wi-Fi network isn’t secure, and your iPhone warns you when Wi-Fi networks have weak security.
Additionally, we have not listed “Enterprise” options in the list below because Enterprise, or RADIUS-server based Wi-Fi security, is uncommon in residential settings and requires additional infrastructure.
Further, please note that depending on your router, the non-Enterprise options may be designated as either “Personal” or “PSK”—PSK stands for “Pre-Shared Key” and indicates that, unlike an Enterprise setup, the security doesn’t rely on an authentication server but instead on the user having the pre-shared key (the Wi-Fi password) to input as their method of authentication. Starting with WPA2, and especially with WPA3, it’s more common to see “Personal” instead of “PSK.”
With those notes in mind, here are the options you’re likely to see on your router.
- Open [Deprecated]: Open Wi-Fi networks have no passphrase. You shouldn’t set up an open Wi-Fi network—seriously, you could have your door busted down by police.
- WEP 64 [Deprecated]: The old WEP protocol standard is vulnerable, and you shouldn’t use it.
- WEP 128 [Deprecated]: This is WEP, but with a larger encryption key size. It isn’t really any less vulnerable than WEP 64.
- WPA-PSK (TKIP) [Deprecated]: This uses the original version of the WPA protocol (essentially WPA1). It has been superseded by WPA2 and isn’t secure.
- WPA-PSK (AES) [Deprecated]: This uses the original WPA protocol but replaces TKIP with the more modern AES encryption. It’s offered as a stopgap, but devices that support AES will almost always support WPA2, while devices that require WPA will almost never support AES encryption. So, this option makes little sense.
- WPA2-PSK (TKIP) [Deprecated]: This uses the modern WPA2 standard with older TKIP encryption. This isn’t secure, and is only a good idea if you have older devices that can’t connect to a WPA2-PSK (AES) network.
- WPA2-PSK (AES): This is the most secure option (outside of the newer WPA3.) It uses WPA2, the latest Wi-Fi encryption standard, and the latest AES encryption protocol. You should use this option unless your router supports WPA3—then use that instead. On some devices, you’ll just see the option “WPA2” or “WPA2-PSK.” If you do, it will probably just use AES, as that’s a common-sense choice.
- WPA/WPA2-PSK (TKIP/AES): Some devices offer—and even recommend—this mixed-mode option. This option enables both WPA and WPA2, with both TKIP and AES. This provides maximum compatibility with any ancient devices you might have, but it also allows an attacker to breach your network by cracking the more vulnerable WPA and TKIP protocols.
- WPA2/WPA3 Personal(AES): Like the WPA/WPA2 hybrid, this mode is designed for backward compatibility. Your WPA2-only devices will connect using WPA2 (AES) and your WPA3 devices will use the more advanced protocol. It may also be labeled as “WPA3 Transitional” or a variation thereof.
- WPA3 Personal (AES): Older routers don’t have WPA3, and older devices can’t use WPA3. But if you have a new router that supports WPA3 and all newer devices, there’s no reason not to switch over entirely to WPA3.
WPA2 certification became available in 2004. In 2006, WPA2 certification became mandatory. Any device manufactured after 2006 with a “Wi-Fi” logo must support WPA2 encryption. WPA3 certification became available in 2018, and any device certified after July 1, 2020, must support WPA3. (Do note the use of certified and not manufactured, a company can still manufacture and sell an older design that was certified before the adoption of a new standard.)
Given that it’s quite likely every Wi-Fi device on your network (including the router itself) was certified and manufactured after 2006, there is no reason you shouldn’t use any security protocol below WPA2-PSK (AES). You should be able to select that option in your router and experience zero issues.
If you have a newer router that supports WPA3, we recommend trying WPA3 (AES) to jump to the highest level of security. If you run into any issues, switch to WPA2/WPA3 Hybrid (AES). This way, the newest devices will use the best security, and the older devices will fall back to WPA2—either way, they’ll be using AES, which is ideal.
If you don’t have a newer router, it’s probably time to recycle it and upgrade to a current Wi-Fi router with up-to-date standards and all the Wi-Fi improvements that come with it. You don’t need to buy a cutting-edge Wi-Fi 7 model, but it’s a great time to jump to Wi-Fi 6 or Wi-Fi 6E if you haven’t already.
WPA and TKIP Will Slow Your Wi-Fi Down
Maybe you’ve been reading along so far and thinking, “I don’t really care that much about security.” While we’d encourage you to be more concerned about Wi-Fi network security, we understand that’s not a pressing priority for everyone.
So here’s a compelling reason to use better Wi-Fi security algorithms everyone can get behind. WPA and TKIP compatability options aren’t just bad from a security standpoint. They can slow down your Wi-Fi network, too.
When you run WPA/TKIP on a router that supports 802.11n and newer, faster standards, it will slow down to 802.11g speeds (54 Mbps) to ensure backward compatibility with older clients. That’s agonizingly slow.
By comparison, even 802.11n (Wi-Fi 4) supports up to 300 Mbps if you’re using WPA2 with AES. Most folks have newer routers now, though. If you have an 802.11ac (Wi-Fi 5), or 802.11ax (Wi-Fi 6) router and you’re using WPA/TKIP, you’re leaving a huge amount of performance on the table.
In Wi-Fi generations, 802.11g is essentially “Wi-Fi 2” and came out in 2003. There’s just no good reason to use a Wi-Fi security standard that insecure, out of date, and slow.
When In Doubt, Always Choose WPA 2 (AES) or WPA3
We’ve said it multiple times so far, but one last time for emphasis. If you’re not sure what setting to pick on your router, always pick the most secure, and for any route made after 2010 or so, that’s WPA 2 (AES) or WPA 3.
On most routers we’ve seen certified prior to 2018, the options are generally WEP, WPA (TKIP), and WPA2 (AES)—with perhaps a WPA (TKIP) + WPA2 (AES) compatibility mode thrown in for good measure. If this is what you’re router offers you, set your router to WPA2 (AES).
On routers certified after 2018 (especially after the July 1, 2020 deadline), you’ll find WPA3 and WPA2/WPA3 compatibility modes. We strongly recommend trying pure WPA3 mode. If everything works, great! You’re rocking the best Wi-Fi security setup you can. If you find there are a few older mission-critical items in your home (like a Wi-Fi thermostat) that won’t play nice with WPS then fall back to WPA2/WPA3 compatibility mode.
But whatever you do, it’s time to shelve all the lesser Wi-Fi security protocols like WEP, WPA, and WPA2 (TKIP) for good.
The Best Wi-Fi Routers of 2023

Best Wi-Fi Router Overall
ASUS AX6000 (RT-AX88U)

Best Budget Router
TP-Link Archer AX3000 (AX50)

Best Cheap Router
TP-Link Archer A8

Best Gaming Router
ASUS GT-AX11000 Tri-Band Router

Best Mesh Wi-Fi Router
ASUS ZenWiFi AX6600 (XT8) (2 Pack)

Best Budget Mesh Router
TP-Link Deco X20

Best Modem Router Combo
NETGEAR Nighthawk CAX80

Best VPN Router
ExpressVPN Aircove

Beat Travel Router
TP-Link AC750

Best Wi-Fi 6E Router
